In today’s digital environment, cyber threats are becoming more advanced and frequent. Businesses of all sizes rely on applications, networks, and cloud systems to manage operations, making cybersecurity a top priority. Organizations utilize vulnerability assessment and pen testing procedures to find and address security flaws before attackers take advantage of them.
Before understanding the lifecycle of these projects, it is important to know what vulnerability assessment and penetration testing actually mean.
What Is Vulnerability Assessment and Penetration Testing?
Vulnerability assessment and penetration testing, commonly known as VAPT, are cybersecurity processes used to identify, analyze, and test security weaknesses in systems, applications, or networks.
Vulnerability Assessment
A vulnerability assessment focuses on finding security flaws, misconfigurations, and weaknesses within IT systems.
It helps businesses:
- Detect vulnerabilities
- Prioritize security risks
- Improve overall security posture
Penetration Testing
Penetration testing, also called ethical hacking, involves simulating real cyberattacks to test how vulnerable systems are to exploitation.
Security professionals attempt to exploit identified weaknesses to understand the potential impact of an attack.
Together, vulnerability assessment & pen testing provide a complete understanding of an organization’s cybersecurity risks.
Why VAPT Is Important for Businesses
Modern organizations face various cyber threats, such as:
- Ransomware attacks
- Data breaches
- Phishing attacks
- Malware infections
- Unauthorized access attempts
A proper VAPT process helps businesses:
- Identify hidden vulnerabilities
- Prevent cyberattacks
- Protect sensitive data
- Meet compliance requirements
- Improve customer trust
Many organizations now use VAPT testing services or pentest as a service solutions to strengthen cybersecurity continuously.
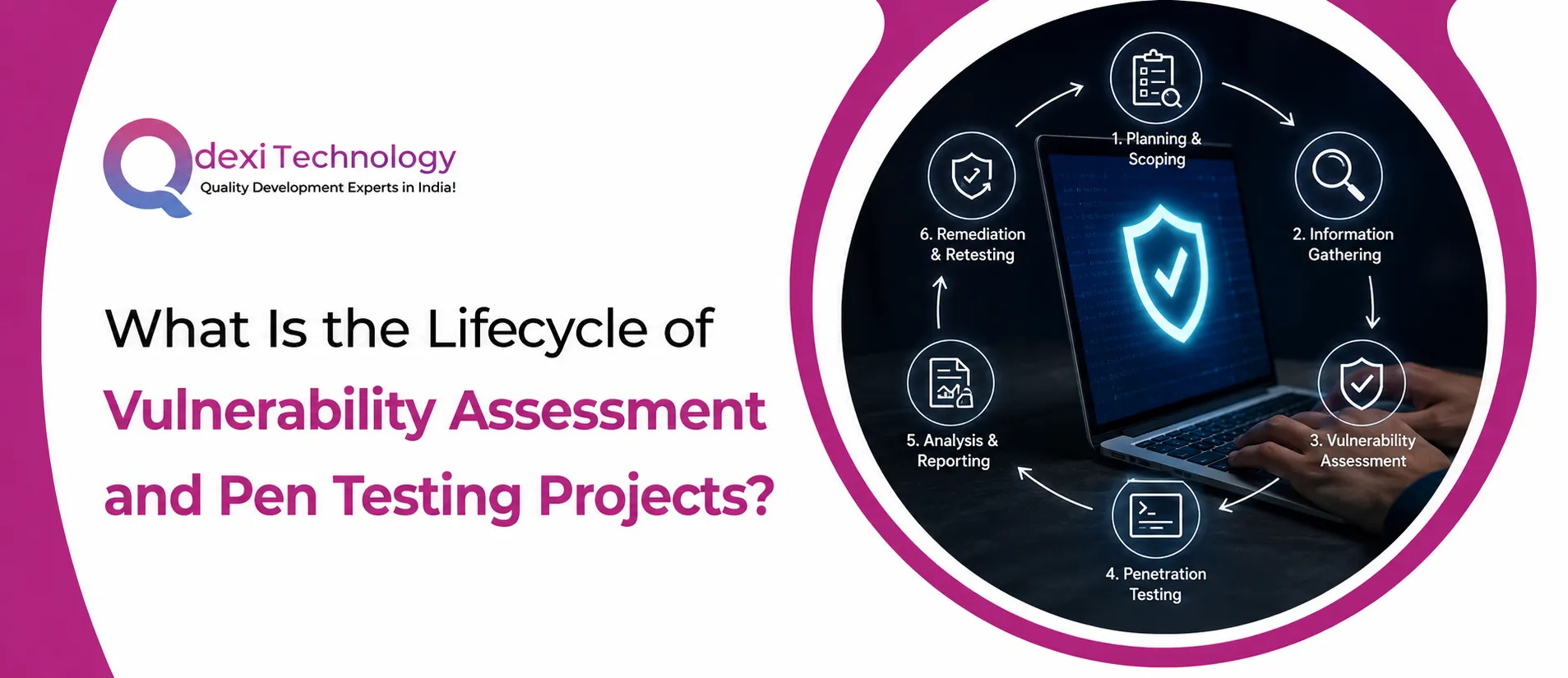
Lifecycle of Vulnerability Assessment and Pen Testing Projects
The lifecycle of vulnerability assessment and penetration testing projects includes several important phases. Each stage helps ensure that security risks are identified, tested, and resolved effectively.
1. Planning and Scope Definition
The first phase of a VAPT project involves defining the project scope and objectives.
This stage includes:
- Identifying target systems
- Defining testing boundaries
- Understanding business goals
- Setting timelines and permissions
Organizations and security teams discuss what needs to be tested, such as:
- Web applications
- Mobile applications
- Networks
- APIs
- Cloud environments
Proper planning ensures that the assessment is organized and aligned with business requirements.
2. Information Gathering and Reconnaissance
In this phase, security professionals collect information about the target systems.
This may include:
- IP addresses
- Domain details
- Open ports
- Network architecture
- Operating systems
The goal is to understand how the systems are structured before testing begins.
Reconnaissance can be
- Passive (collecting publicly available information)
- Active (directly interacting with systems)
This phase forms the foundation of effective vulnerability assessment & pen testing.
3. Vulnerability Identification
After gathering information, security experts use automated tools and manual techniques to identify vulnerabilities.
Common issues discovered include:
- Weak passwords
- Misconfigured servers
- Outdated software
- Unpatched systems
- Insecure APIs
This stage is the core of the vulnerability assessment process.
Organizations using professional VAPT testing services often benefit from advanced scanning tools and expert analysis.
4. Vulnerability Analysis and Risk Assessment
Not every vulnerability poses the same level of risk. During this stage, identified issues are analyzed and prioritized based on severity.
Security teams evaluate:
- Likelihood of exploitation
- Business impact
- Data sensitivity
- System criticality
Vulnerabilities are typically classified as the following:
- Low risk
- Medium risk
- High risk
- Critical risk
This helps businesses focus on fixing the most dangerous threats first.
5. Penetration Testing and Exploitation
This phase involves actively testing vulnerabilities to determine whether attackers can exploit them successfully.
Ethical hackers simulate real-world attacks to:
- Gain unauthorized access
- Escalate privileges
- Access sensitive information
- Test system defenses
This practical testing process differentiates penetration testing from basic vulnerability scanning.
Modern pentest as a service solutions often provide continuous and on-demand penetration testing for businesses.
6. Reporting and Documentation
After testing is completed, security teams prepare detailed reports explaining the findings.
A typical VAPT report includes:
- Identified vulnerabilities
- Risk levels
- Exploitation details
- Screenshots and evidence
- Recommended fixes
These reports help IT teams understand security gaps and take corrective actions.
Clear documentation is one of the most important outcomes of vulnerability assessment and penetration testing projects.
7. Remediation and Fixing Vulnerabilities
Once vulnerabilities are identified, businesses must address and fix them.
Remediation may involve:
- Updating software
- Changing configurations
- Applying security patches
- Strengthening access controls
Security teams often work closely with developers and IT administrators during this phase.
8. Retesting and Validation
After fixes are implemented, systems are retested to confirm that vulnerabilities have been resolved successfully.
This step ensures:
- Security gaps are closed
- Fixes are effective
- No new issues were introduced
Retesting is a critical part of the vulnerability assessment & pen testing lifecycle.
Benefits of VAPT Testing Services
Organizations increasingly rely on professional VAPT testing services because they provide the following:
- Expert security analysis
- Continuous monitoring
- Advanced testing methodologies
- Faster threat detection
- Regulatory compliance support
These services help businesses strengthen cybersecurity and reduce risks.
Future of VAPT and Pen Testing
Cybersecurity is constantly evolving, and future VAPT solutions will become more advanced with:
- AI-powered threat detection
- Automated penetration testing
- Cloud security assessments
- Continuous security validation
Businesses adopting modern pentest as a service platforms will be better prepared for evolving cyber threats.
Conclusion
Understanding the lifecycle of vulnerability assessment and penetration testing projects is essential for organizations aiming to improve cybersecurity. From planning and reconnaissance to exploitation, remediation, and retesting, every stage plays a critical role in protecting systems and data.
By investing in professional VAPT testing services and modern pentest as a service solutions, businesses can proactively identify vulnerabilities, reduce risks, and build stronger cybersecurity defenses against modern threats.
#VAPT #VulnerabilityAssessment #PenetrationTesting #CyberSecurity #EthicalHacking #VAPTTestingServices #PentestAsAService #SecurityTesting #CyberThreats #DataSecurity #NetworkSecurity #ApplicationSecurity #RiskManagement #InformationSecurity #CyberProtection